IT Insights & Company News
We publish our articles, case studies, and industry insights on LinkedIn to engage with the professional community.
Follow us on LinkedInFilter & sort articles
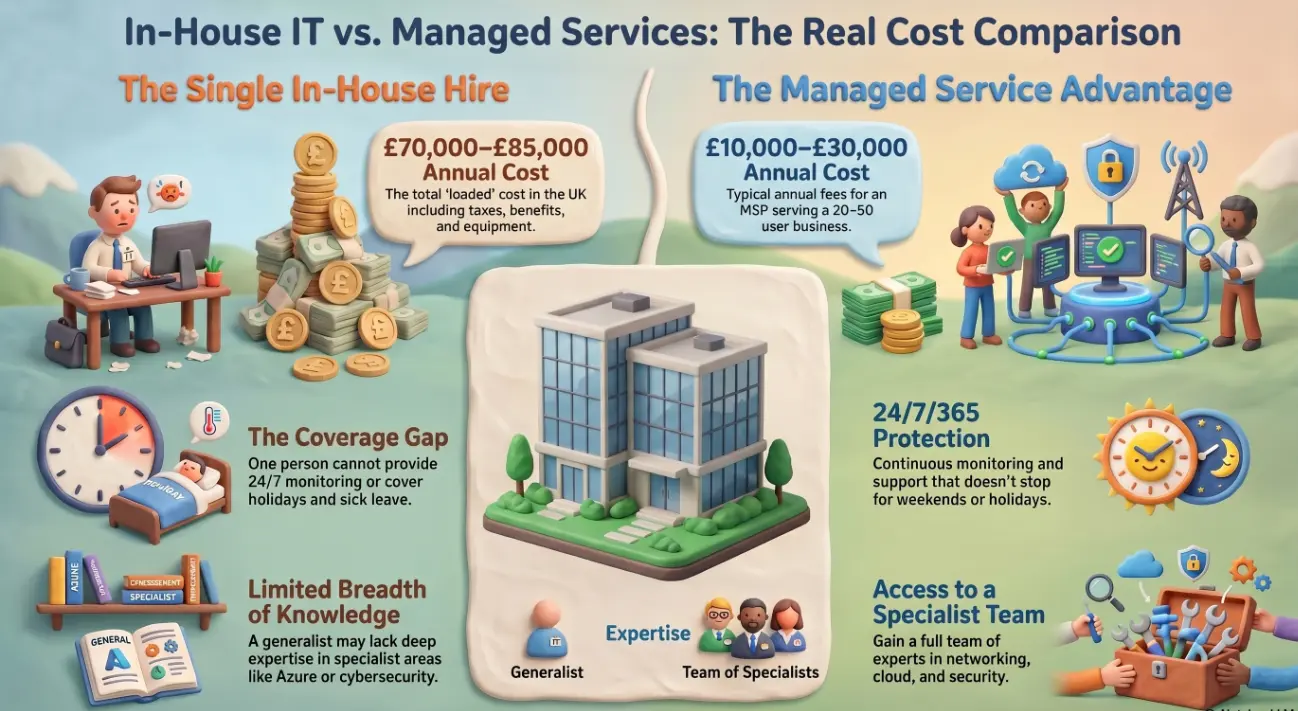
Managed IT services vs in-house IT for small business
A small business owner in Dublin hired her first full-time IT person two years ago. The salary was £45,000. Add employer National Insurance, pension contributions, a laptop, training budget, and the Microsoft certifications she needed him to hold — and the real cost was closer to £62,000 annually....
....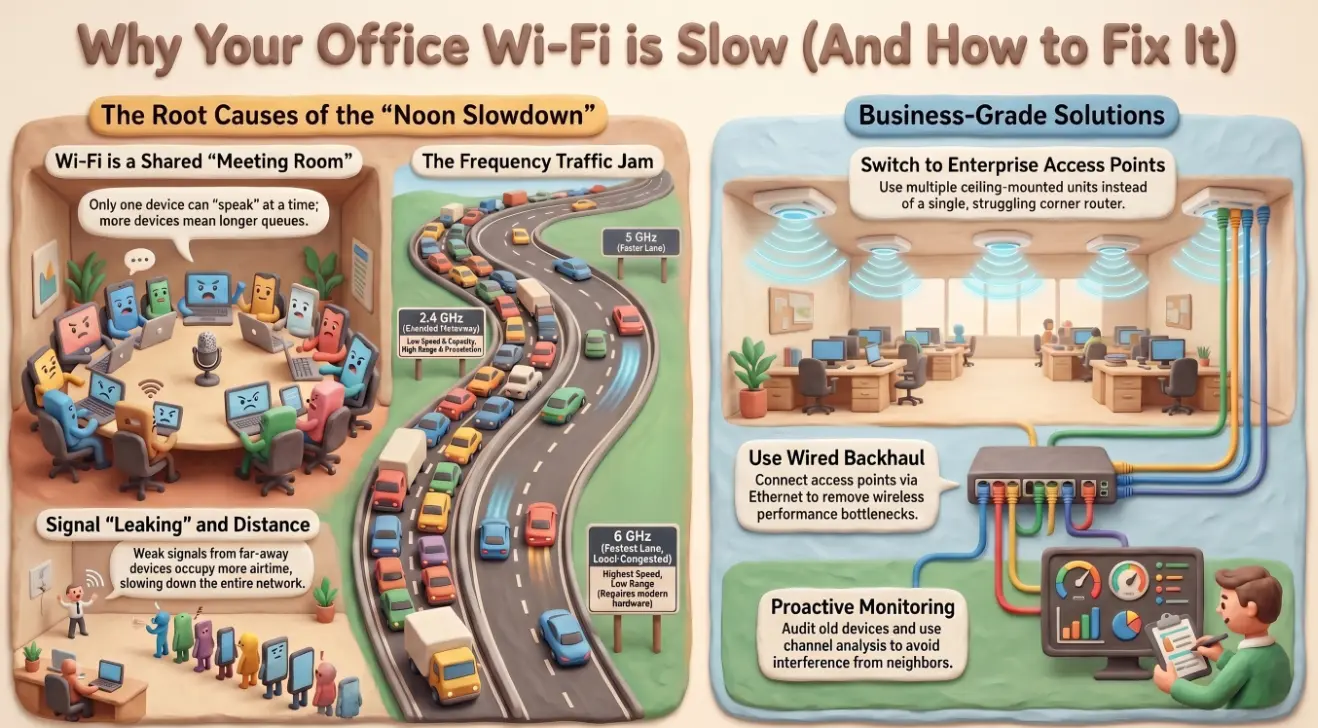
Why is office Wi-Fi slow — and how to fix it
You call your internet provider. You wait on hold for twenty minutes. A technician runs a speed test and tells you your connection is fine — 200 megabits, exactly what you're paying for. You hang up. The video call still buffers. The file upload still crawls. And every day at noon....
....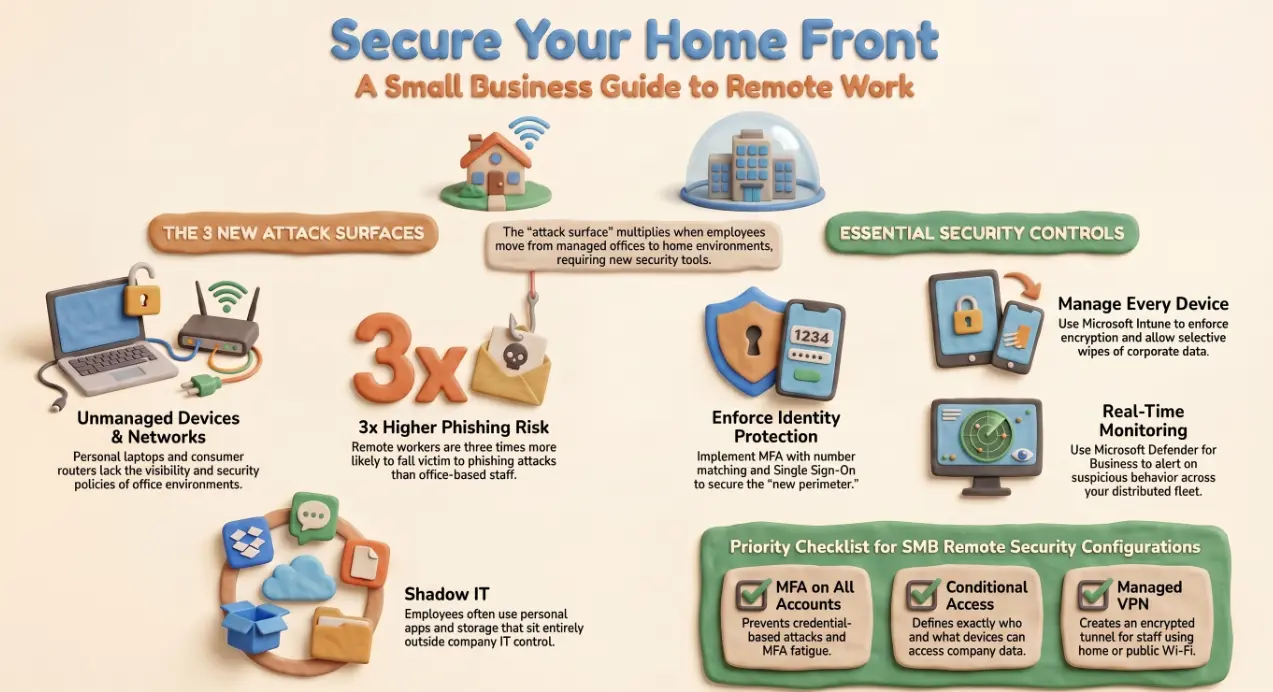
Secure remote work setup for small business: a guide
Remote workers are three times more likely to fall victim to a phishing attack than their office-based colleagues. That figure isn't a coincidence — it reflects something structural. The office environment has a managed network, physical access controls, IT visibility, and colleagues nearby to sanity-check a suspicious email. The home environment has a consumer router, a personal device possibly shared with family member....
....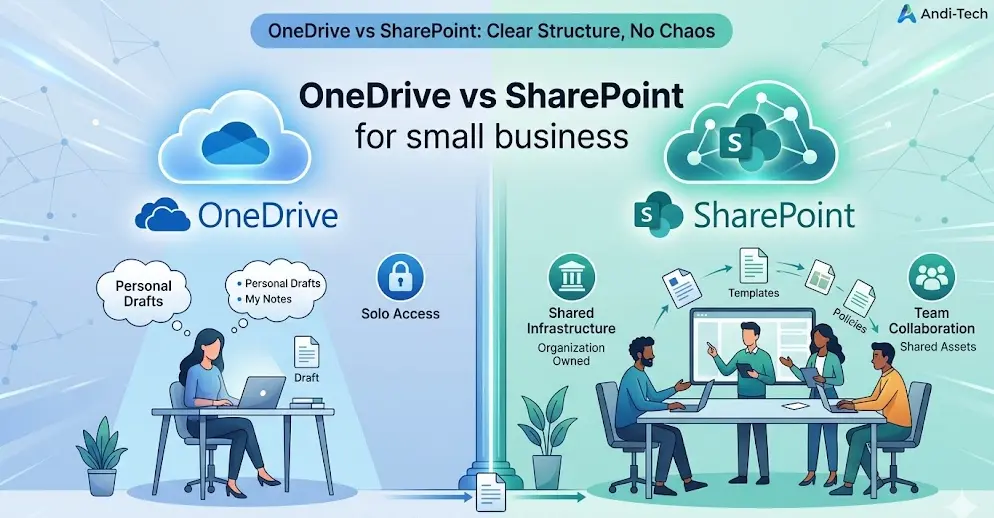
OneDrive vs SharePoint for small business: which to use
A marketing manager saves her campaign assets to OneDrive. A colleague uploads the same files to a SharePoint site. A third team member can't find either version and starts a new folder on their desktop. By Thursday, there are four copies of the same document, nobody is sure which is current....
....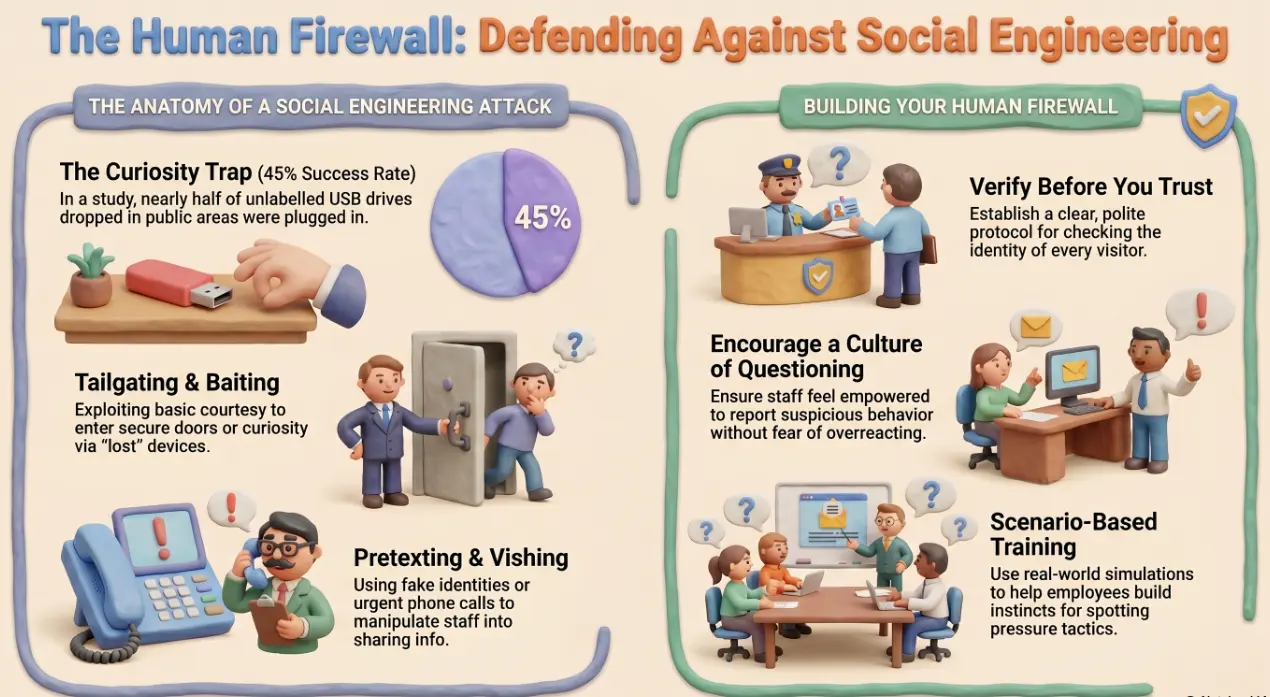
Social engineering attacks: how to protect your business
In 2016, researchers from the University of Illinois dropped 297 USB drives across the campus of a large organisation. The drives were unlabelled, ordinary-looking, and left in car parks, corridors, and common areas. Nearly half were plugged into company computers within hours....
....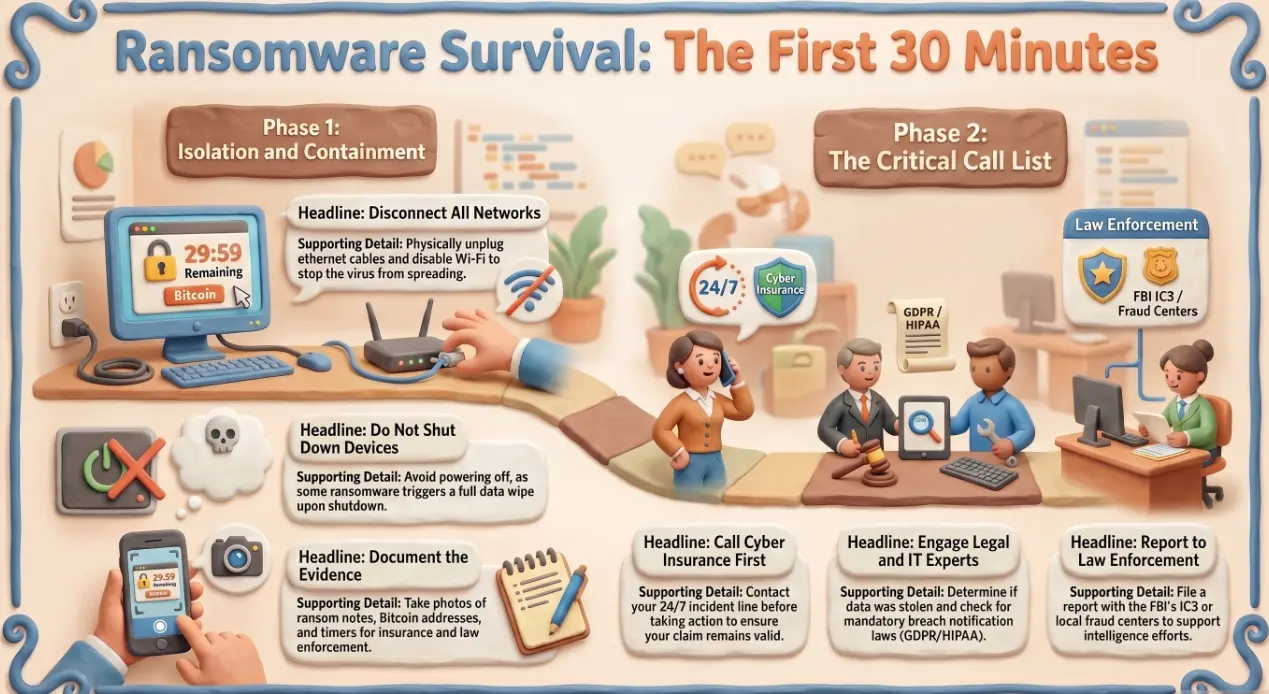
Ransomware recovery plan for small business
It's 8:47am on a Monday. You unlock the office, flip on the lights, and sit down at your desk. The screen is already on — but it isn't showing your desktop. It's showing a red countdown timer, a Bitcoin wallet....

Microsoft Intune for small business device management
A sales manager boards a train in Chicago, laptop in bag. By the time she reaches her destination, the bag is gone. On that laptop: a CRM export with 3,000 client records, a folder of contract drafts, and cached Microsoft 365 credentials. The IT manager gets the call....
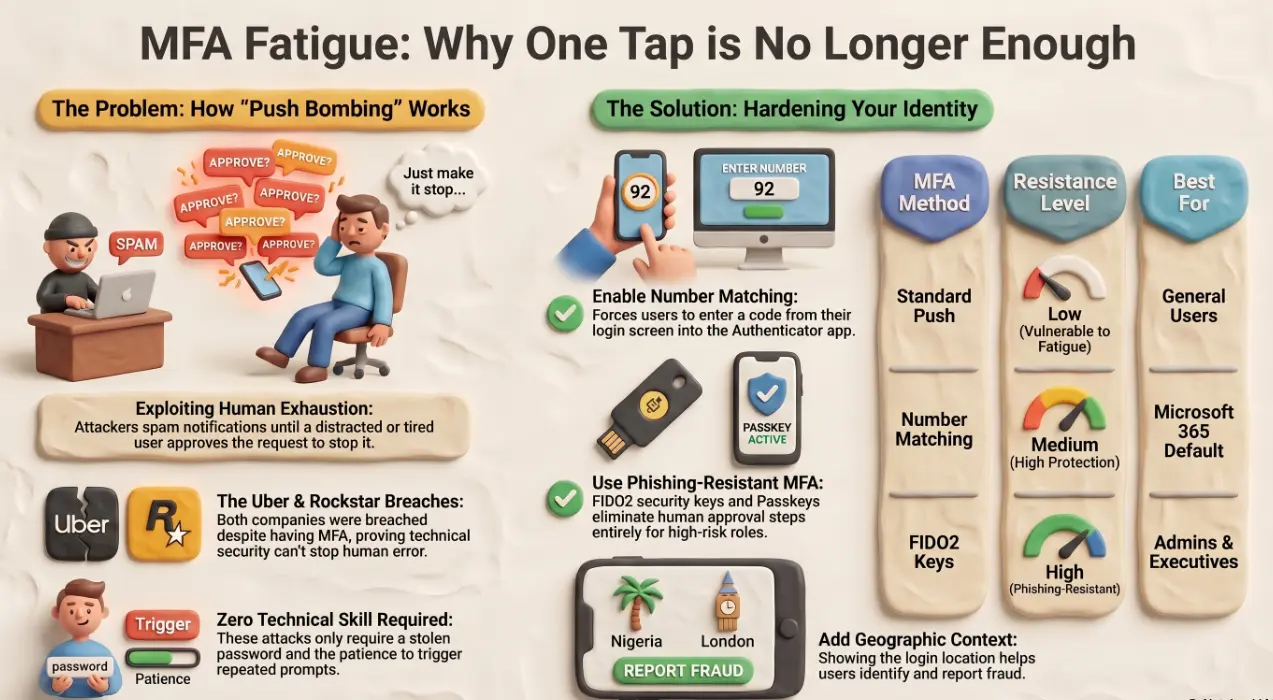
MFA fatigue attacks: why MFA alone is no longer enough
In September 2022, an 18-year-old contractor gained full administrative access to Uber's internal systems. He didn't exploit a zero-day vulnerability. He didn't break any encryption. He sent an employee repeated MFA push notifications at 1am until the employee, exhausted, approved one — and then messaged the attacker on WhatsApp to say he'd stop if the notifications did. That was enough....
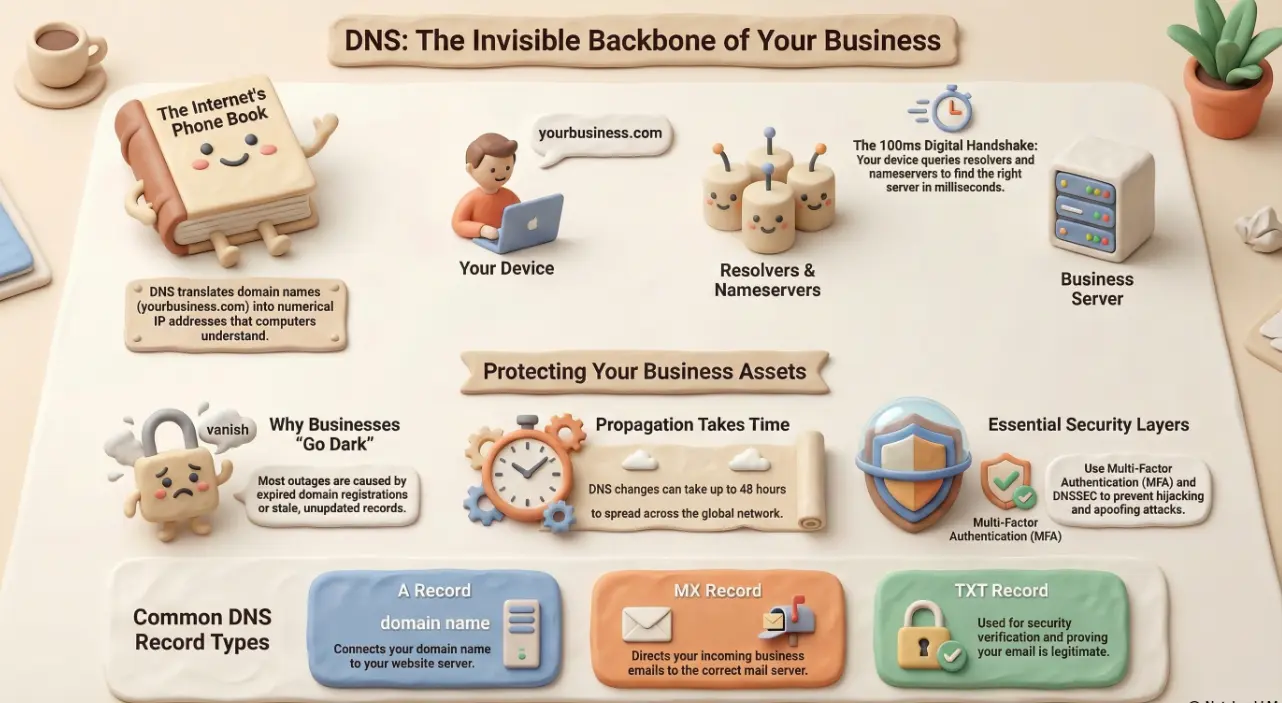
What is DNS and why it matters for your business
It was a Monday morning when the calls started. A small accounting firm in Manchester had spent the weekend at a trade show handing out business cards — and now, every single prospect who typed their web address into a browser got an error....
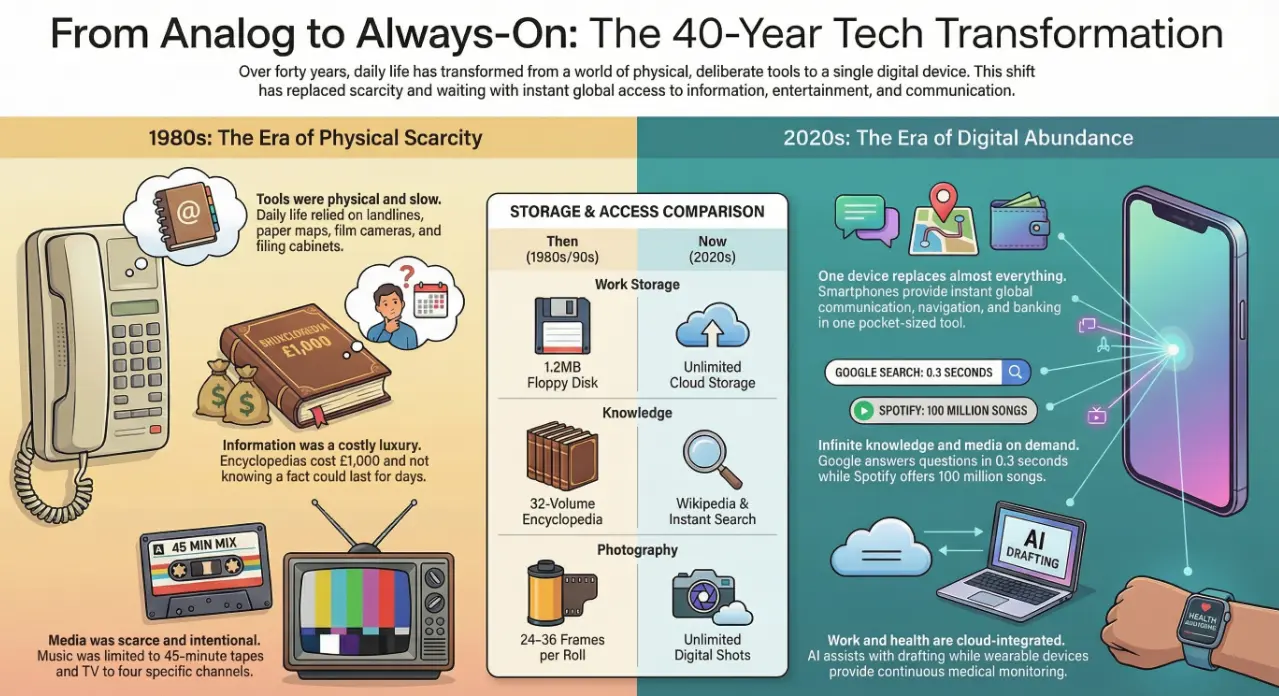
From physical tools to digital life — a transformation in one generation
Waking up in 1985 meant no screen, no notification — just an alarm clock with a real bell. Every tool of daily life was physical, deliberate, and slow. Forty years later, a single glass rectangle in your pocket has replaced almost all of it....
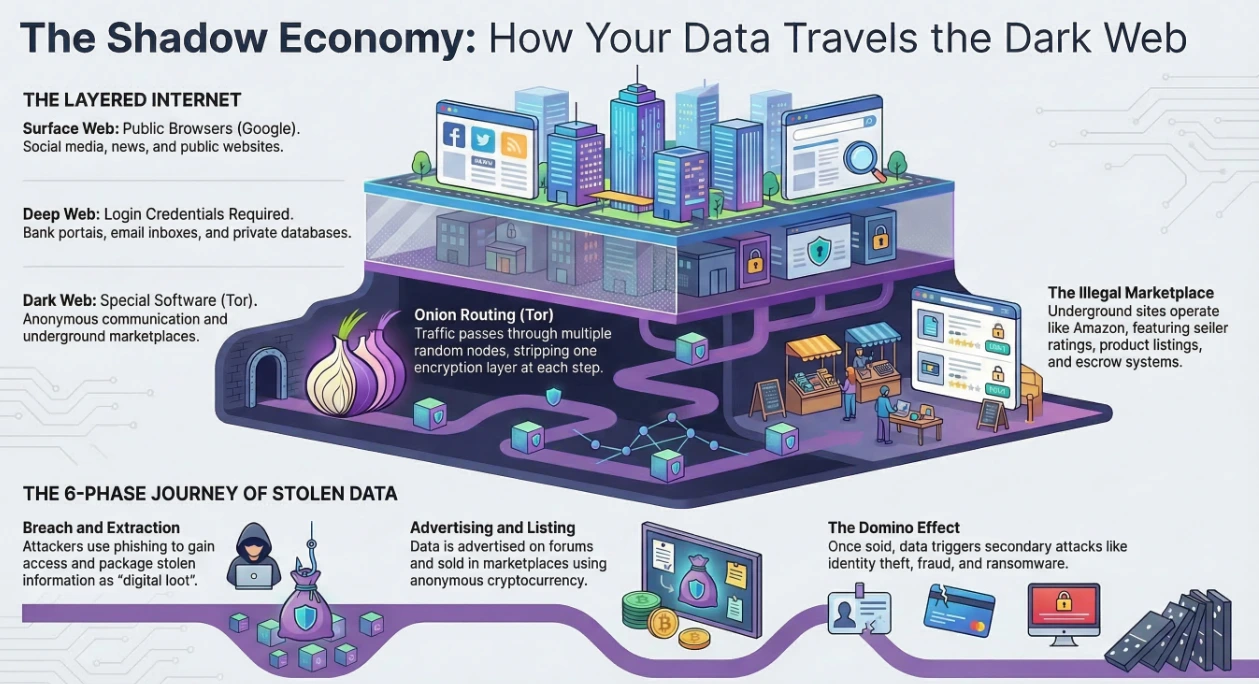
Understand what the Dark Web is
Imagine the internet as a massive city. Most people live in the bright downtown area — Google, YouTube, LinkedIn, news sites. This visible part is called the Surface Web....
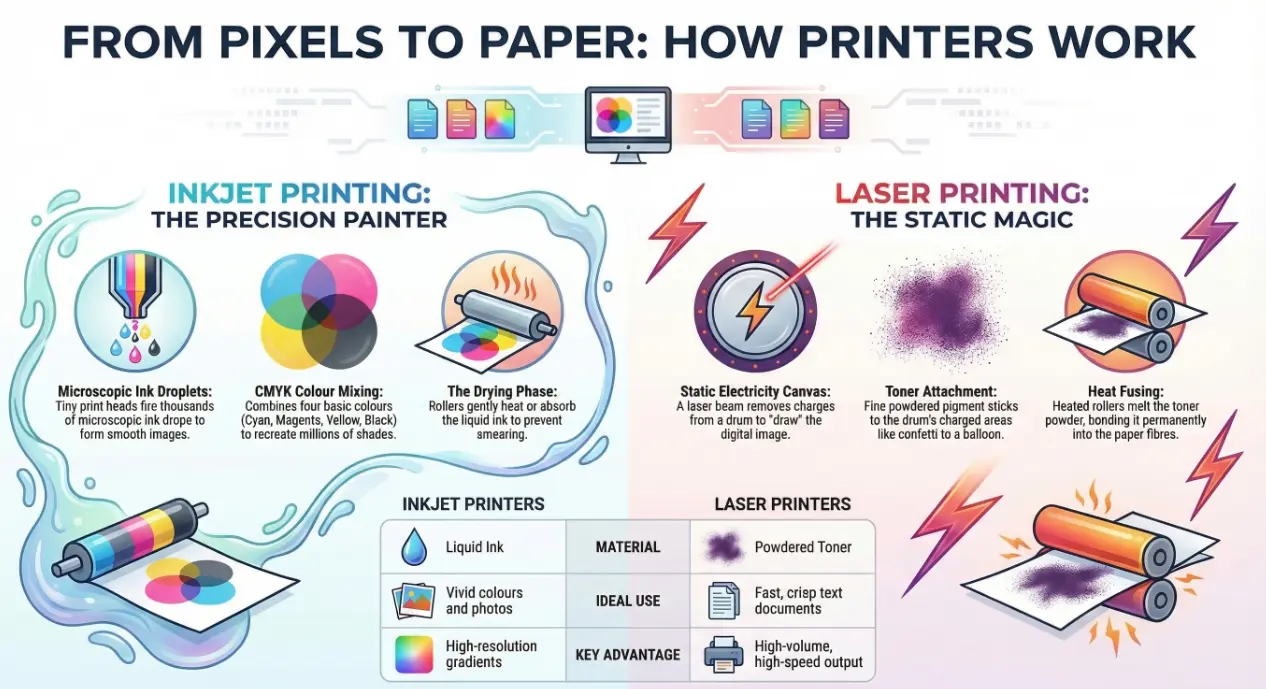
A Simple Story from Digital to Paper
Imagine you're a chef. Your customer sends in a picture of a beautiful cake they want — colors, shapes, everything perfect. You can't just guess the cake — you need a recipe....
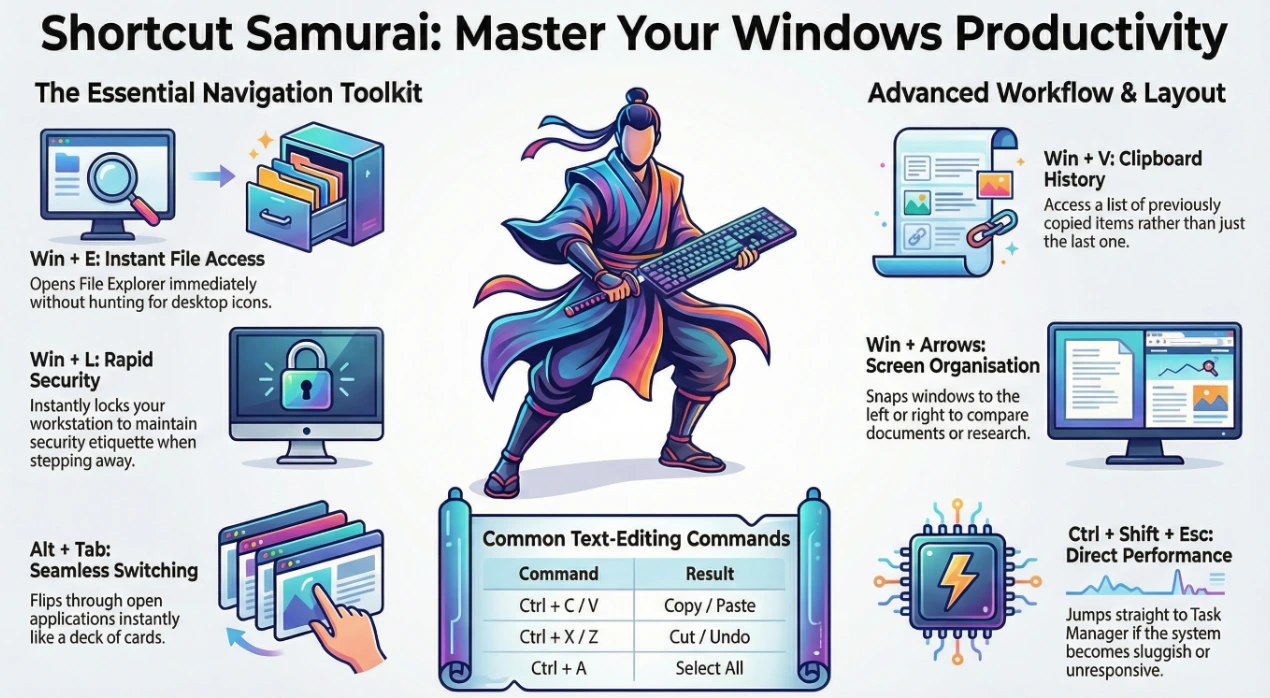
Shortcut Samurai
Have you ever watched someone type like a Jedi with the Force? One minute they're opening folders, switching apps, snapping windows into place — all without touching the mouse....
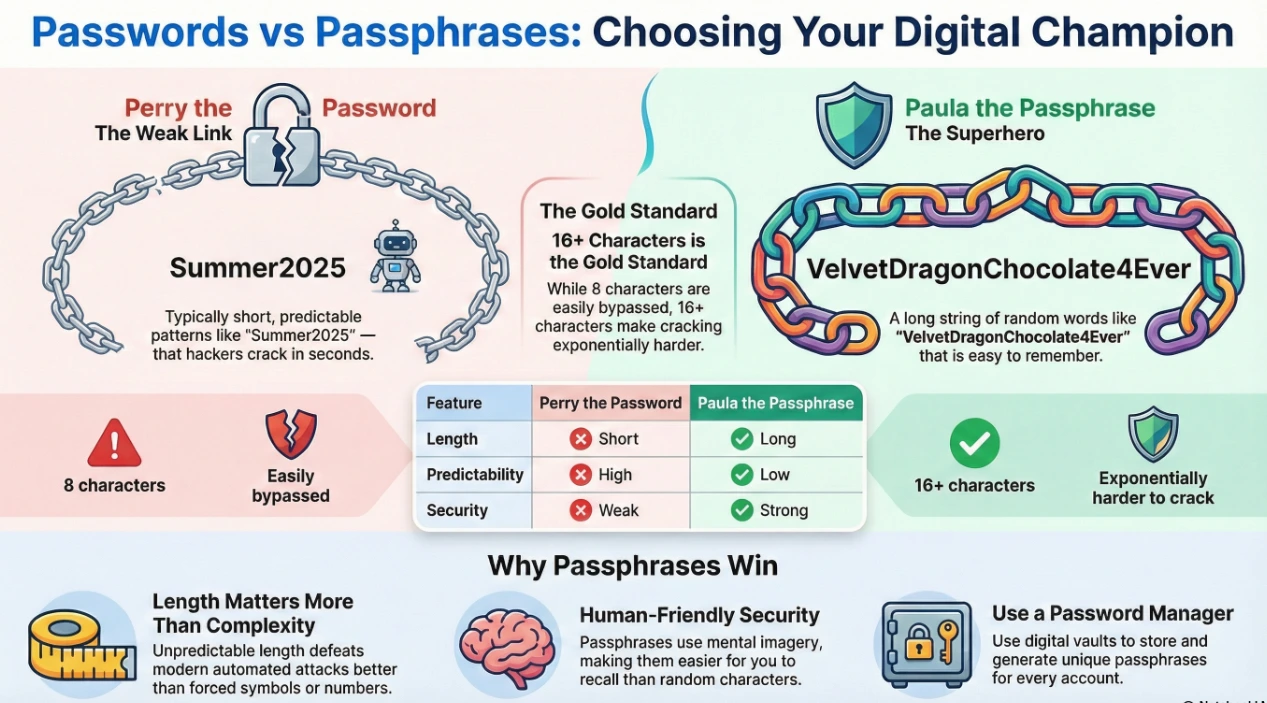
Passwords vs Passphrases explained
In one corner, wearing a tiny mask and a flimsy paper shield, stands Perry the Password. And in the other corner, towering like a heroic librarian with a reinforced vault of knowledge....
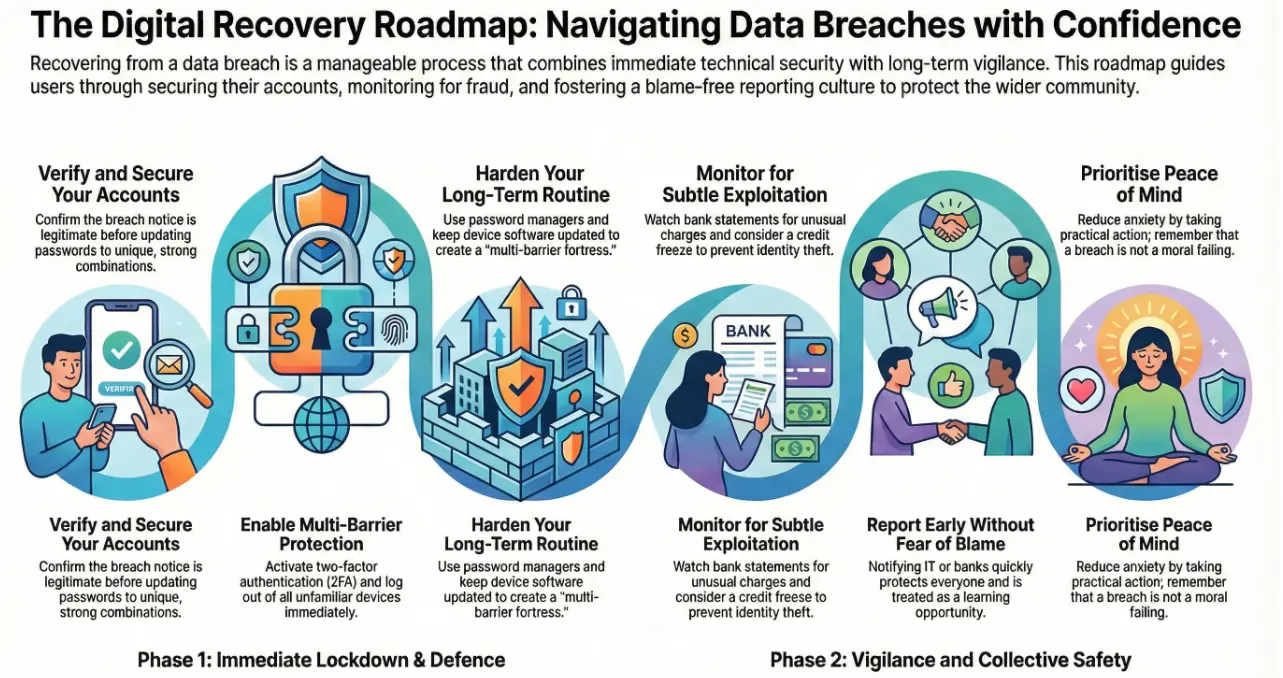
What To Do After a Data Breach
A clear, human-friendly guide explaining exactly what to do after a data breach, how to secure your accounts, protect your peace of mind, and recover safely....
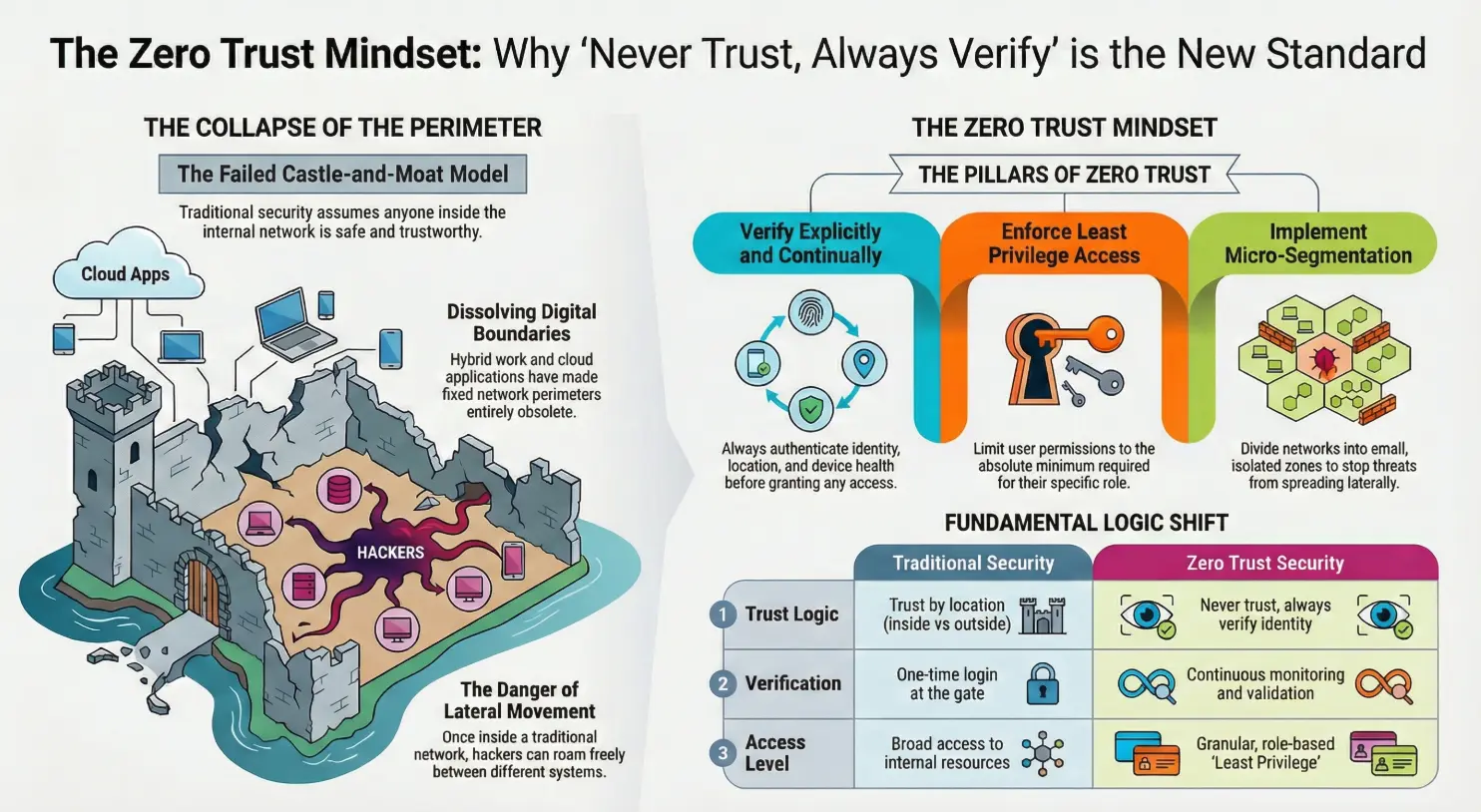
Trust nothing. Verify everything
Imagine this: you walk into a café you visit every day. The barista recognizes you, smiles, and hands you your favourite drink without checking your name on the order....
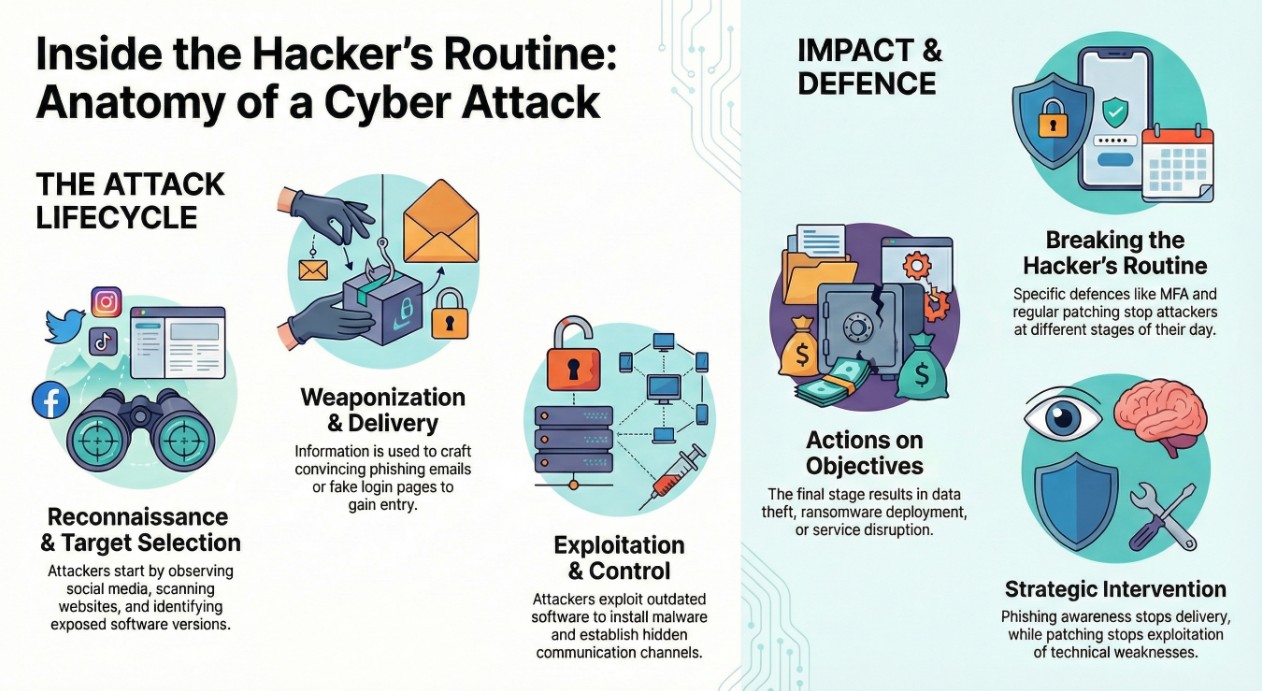
A Day in the Life of a Hacker
Explore how hackers think and operate by walking through a typical day in the life of a digital attacker. Learn how cyber attacks unfold and how to stop them....

Secure your connection wherever you are
Whether you're working remotely, traveling, or using public Wi-Fi, your internet connection can expose more information than you realise....

Stay cyber-safe while enjoying the Christmas holidays
The holiday season is magical ✨. Flights are booked, hotels are reserved, and your out-of-office reply is ready. But while you're relaxing, cybercriminals know something important....

Microsoft Office 365 Explained
Office 365 is a cloud-based productivity platform that combines familiar Office apps with email, file storage, collaboration tools, and enterprise-grade security....

Encryption & BitLocker – Stay Secure
Imagine you have a magic suitcase. Inside you keep your diary, your photos, your bank PIN list, and some secrets. When the suitcase is locked with a key that only you have — they only see gibberish....

A friendly journey into what's happening inside your PC
Imagine your computer as a tiny city inside a box. Every time you click an icon, type a word, or open a game, millions of miniature workers spring into action....

When Thanksgiving and IT Meet at the Same Table
Thanksgiving and IT feel like they live in completely different worlds — one is full of food and family, the other is full of tickets, log files, and that one printer that always chooses violence....

Email traveling through the internet
Imagine sending a simple email to a friend. You hit Send, the window closes, and it feels like nothing dramatic happened. But that tiny click wakes up an entire hidden universe....

Microsoft 365 – Subscription Plans Explained
In today's digital world, productivity left to traditional desktop software feels a bit like using a paper map in a smartphone era....
The Rise of Freelancing: Your Gateway to Independent Work
Freelancing is the modern way of working where individuals offer their skills and services to clients independently — without being tied to one employer....
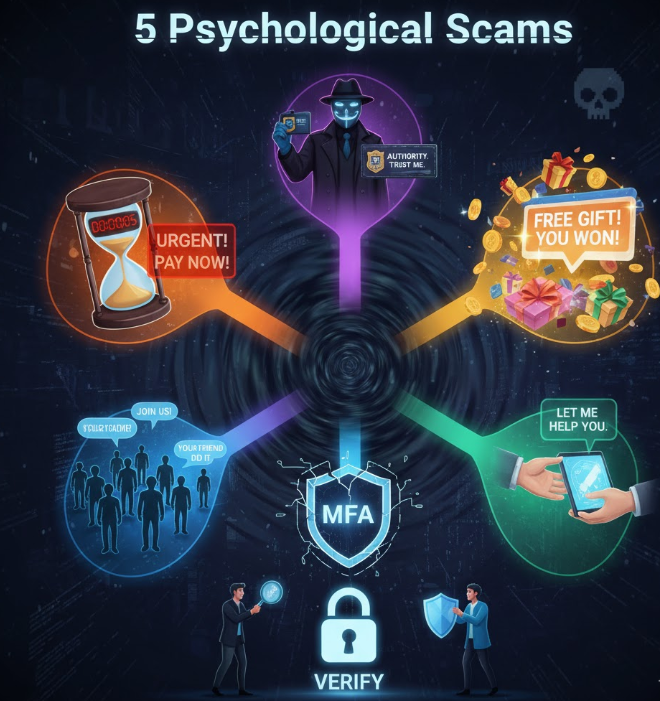
5 Psychological Tricks Hackers Use to Scam You
Hackers often create a false sense of urgency — "Your account will be suspended!", "Pay this now or lose everything!" — to push you into making a quick decision without thinking....

Differences Between Cloud Storage Services
Cloud storage isn't just a nice-to-have anymore — it's central to how we work, share and protect files. Whether you're an individual or a business leader, the right service makes a big difference....

5 Simple Cybersecurity Habits Everyone Should Have
Cybersecurity isn't just for tech experts anymore — it's for everyone. Whether you're checking emails, shopping online, or managing business accounts, one wrong click can lead to a data breach....

Password Managers Explained: Why You Should Use Them (and Which Are Best)
In the digital age, we juggle dozens of logins — banking, cloud services, work platforms, and social media. Using the same password everywhere is a major risk....

How to Spot a Fake Email in 5 Seconds – Real-Life Examples + Quick Checks
Picture this: ☕ You open your laptop, and there it is — an email warning that your account will be suspended unless you act right now....

AI Tools That Can Make Your Workday Easier
Artificial Intelligence is no longer a futuristic concept — it's already part of many tools we use every day. From drafting emails to analysing data, AI saves time and reduces repetitive work....
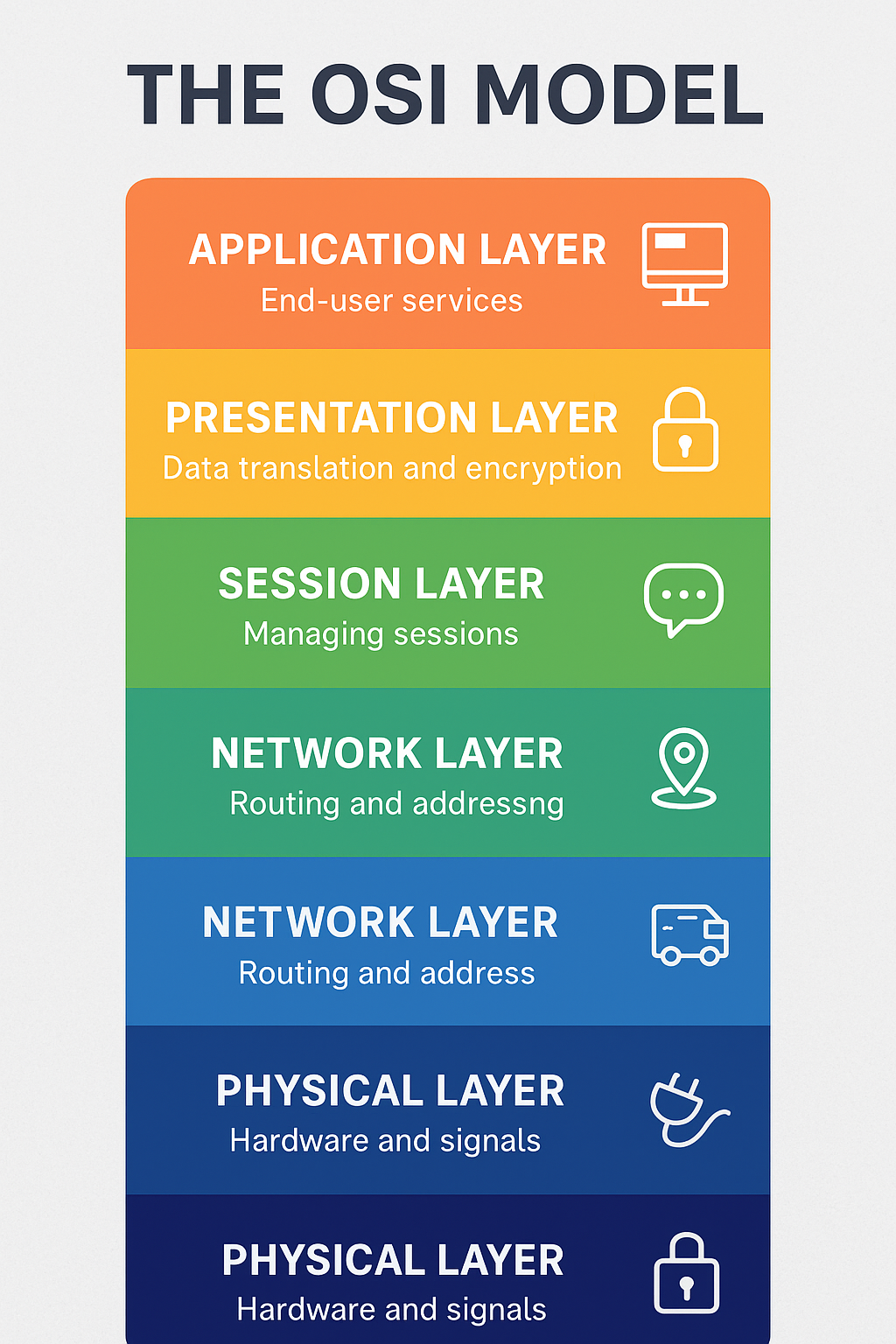
Understanding the OSI Model – A Simple Guide for Everyone
Have you ever wondered how your message, email, or video call travels across the internet? Behind the scenes, there's a system that makes all communication possible: the OSI Model....
Don't Miss Our Latest Updates
Follow Andi-Tech on LinkedIn for real-time IT insights, industry news, and expert tips delivered directly to your feed.
Follow on LinkedIn