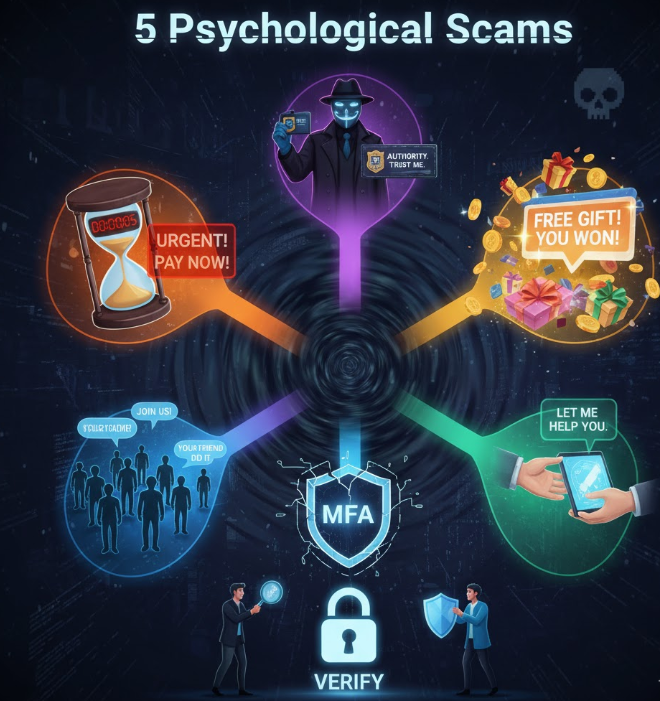
Recognise the psychological games behind cyber scams and defend yourself.
🧠 5 Psychological Tricks Hackers Use to Scam You
⏳ 1. Urgency & Panic Triggers
Hackers often create a false sense of urgency—“Your account will be suspended!”, “Pay this now or lose everything!”, “Immediate action required!”—to push you into making a quick decision without thinking. This taps into your fear and gets you to act impulsively rather than verifying the message.
Tip: Pause before you click. If it’s urgent, call the sender using a known contact, not the one in the email.
🎩 2. Authority Impersonation
Scammers impersonate people you trust—your boss, a vendor, IT support, or a government agency. Because the message seems to come from someone in authority, you’re more likely to comply.
Tip: Always verify unexpected requests. If “IT support” emails you asking for credentials or access, call your internal help-desk to confirm.
🎁 3. Reward or Free-bie Baiting
“We have a free gift for you!”, “Click for your bonus!”, or “Congratulations, you won!” are used to appeal to greed or curiosity. Scammers know these emotional triggers work to bypass checks.
Tip: If it sounds too good to be true— it probably is. Don’t click links promising unexpected rewards.
🤝 4. Social Proof & Familiarity
Hackers may use tactics like “Everyone in your department already signed up”, “Your colleague sent this link” or build familiarity over time via social networks. They exploit the human tendency to trust what others trust.
Tip: Don’t rely solely on familiar names. Check sender email addresses for subtle differences, and hover over links before clicking.
🤫 5. Helpfulness & Reciprocity
Scammers pose as helpful – tech support, friendly colleague, or someone offering assistance. Because you feel obliged or want to be helpful, you comply. Giving info or access seems natural, but it’s a trap.
Tip: Never give control of your device or credentials just because someone asks—even if they claim they’re “helping”.
✅ What You Should Do
- Always verify unexpected requests using known contact methods.
- Enable multi-factor authentication (MFA) for all important accounts.
- Educate your team: nearly half of cyber incidents begin with human manipulation.
- Foster a culture where “questioning” is acceptable—even if the request seems harmless.
📩 Need help strengthening your organisation’s cybersecurity?
At Andi-Tech, we provide tailored cybersecurity training, awareness programs and IT solutions to mitigate the human risk behind cyber-attacks.
📩 Contact us at info@andi-tech.com — let’s make your organisation safer together.