Understanding how attackers think helps us stop them 🧠🔐
🕶️ The Digital Stakeout: How Hackers Plan Like Burglars to Target Your Routine
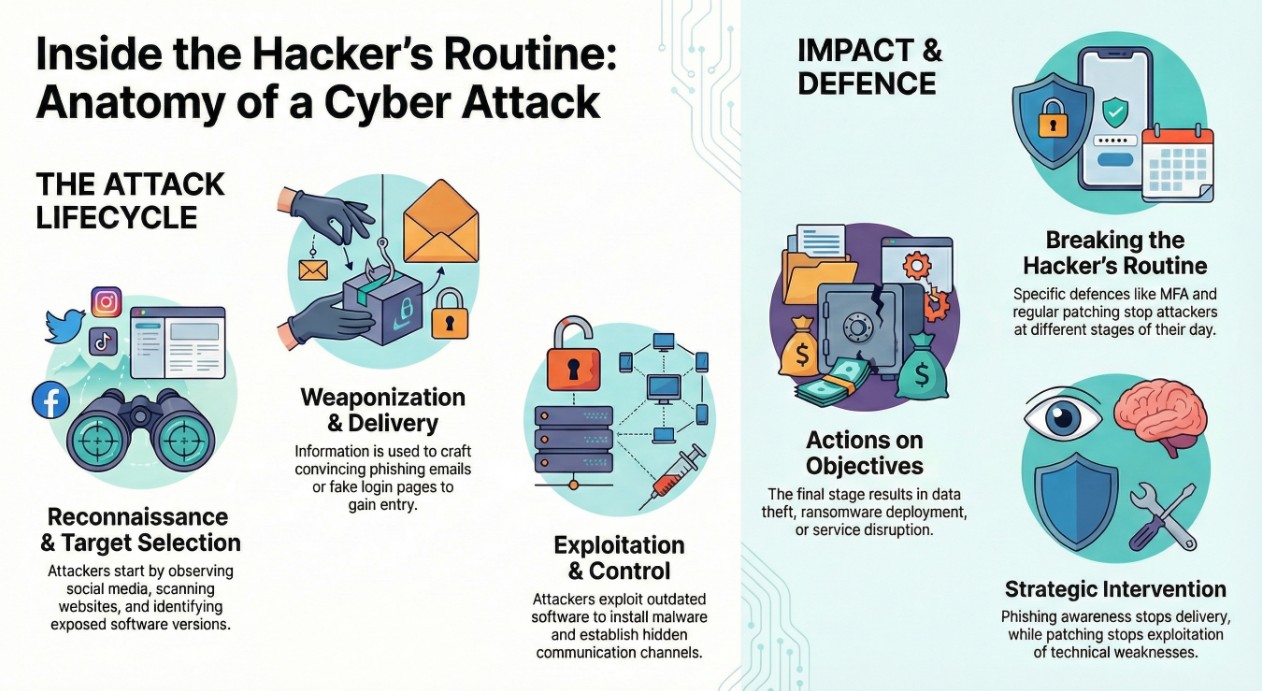
Cyber attacks don’t start with dramatic chaos and frantic keyboard typing like in the movies. They start quietly — with curiosity, patience, and a routine that mirrors your own.
Your morning likely begins the same way most days: ☕ a sip of coffee, checking your email, logging into work systems, and skimming the headlines. It’s comforting. It’s predictable.
Somewhere else, a hacker is starting their day too. But they aren't drinking coffee and reading the news. They are watching you read yours.
Real hacking is methodical. It’s structured around specific stages — very much like a professional burglar planning a break-in. Understanding this playbook removes the mystery and gives you the advantage.
🧭 Morning: The Casing (Reconnaissance)
A smart burglar never runs up to a house and kicks in the door. They watch first. They note routines, unlocked windows, and signs of weak security.
The Digital Routine: Hackers begin the same way — by observing. Before any alarm triggers, they map your digital footprint.
- Scanning company websites and domains
- Reviewing LinkedIn for employee names and roles
- Identifying outdated software and exposed services
They are building a blueprint of your digital home before you’ve finished your first cup of coffee.
🛠️ Midday: Preparing the Tools (Weaponization & Delivery)
Once a burglar identifies a weak lock, they don’t rush in — they prepare the right tool or disguise.
The Digital Routine: Information becomes action. Attackers craft weaponized documents or fake login pages that look identical to services you trust.
These tools are delivered through convincing disguises:
- Urgent invoice emails
- Missed delivery notifications
- Security warnings that feel “important”
One convincing email. One careless click. That’s often all it takes.
💥 Afternoon: Slipping Inside (Exploitation & Installation)
The door opens. The burglar slips inside quietly — not to steal immediately, but to make sure they can stay hidden.
The Digital Routine: When delivery succeeds, attackers exploit software weaknesses or human trust to gain access.
- 💻 Silent malware installation
- 🔑 Creation of backdoors
- 📁 Persistence mechanisms for long-term access
Access alone isn’t enough. Staying unnoticed is the real objective.
🌐 Late Afternoon: Moving Room to Room (Command & Control)
Now comfortable inside, the burglar moves quietly through the house, searching for where the real valuables are stored.
The Digital Routine: Compromised systems establish hidden command-and-control channels back to the attacker.
- Lateral movement between systems
- Credential harvesting
- Data discovery and staging
This is how a small breach becomes a major incident.
🌒 Evening: The Heist (Actions on Objectives)
The burglar strikes when no one is watching — stealing valuables, damaging property, or vanishing silently.
The Digital Routine: This is the final stage where impact occurs.
- 📂 Sensitive data theft
- 💣 Ransomware deployment
- 🔐 Credential resale on underground markets
- 🚫 Service disruption
🧠 Why This Story Matters
Hackers are not magicians — they are operators following predictable patterns. And just like homeowners can deter burglars, defenders can break the hacker’s routine.
- Phishing awareness stops attacks at the front door
- Regular patching closes open windows
- Multi-Factor Authentication (MFA) acts like an alarm system and vault door
🔐 Final Thought
Cybersecurity isn’t about fear — it’s about understanding the playbook. Once you recognize the routine, the mystery disappears, and you know exactly where to reinforce defenses.
Ready to Lock Down Your Digital Home?
Andi-Tech helps individuals and businesses detect reconnaissance, prevent intrusions, and respond to real-world cyber threats.
📧 Reach us anytime: info@andi-tech.com